-
Notifications
You must be signed in to change notification settings - Fork 2.6k
New issue
Have a question about this project? Sign up for a free GitHub account to open an issue and contact its maintainers and the community.
By clicking “Sign up for GitHub”, you agree to our terms of service and privacy statement. We’ll occasionally send you account related emails.
Already on GitHub? Sign in to your account
NIFI-6301 - Added a SafeXMLConfiguration which disables XML DTDs whic… #3507
Conversation
|
Reviewing... |
| private static final String XXE_ERROR_MESSAGE = "XML configuration file contained an external entity. To eliminate XXE vulnerabilities, NiFi has external entity processing disabled."; | ||
|
|
||
| @Override | ||
| public void initFileLocator(FileLocator loc) { |
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
Moving public method below constructors.
|
|
||
| @Override | ||
| public void read(Reader in) throws ConfigurationException, IOException { | ||
| try { |
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
I refactored this duplicate code into a private method (see d67d6e4).
|
|
||
| try { | ||
| // Act | ||
| // Service will fail to enable because test-xxe.xml contains a DTD |
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
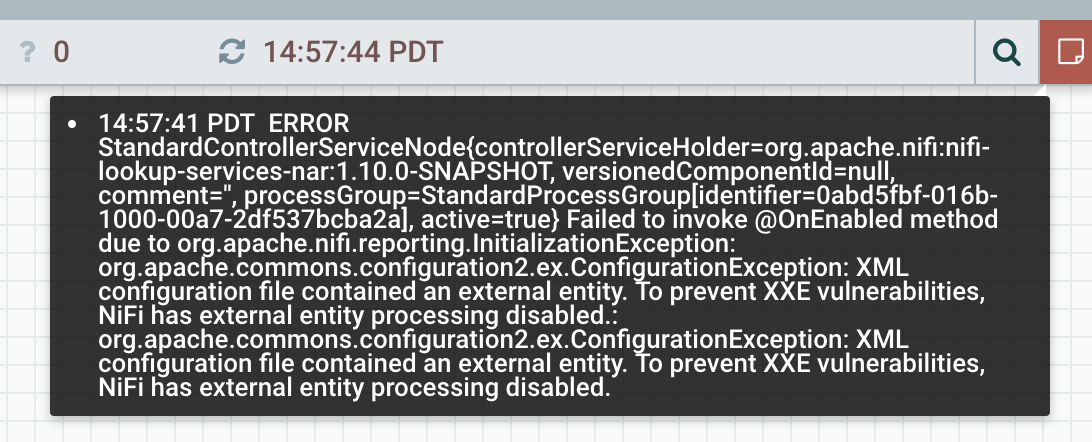
When I run the actual NiFi instance, the service is enabled. There is a bulletin shown, and a stacktrace in the error log, but the service is enabled.
2019-05-30 14:59:20,528 ERROR [Timer-Driven Process Thread-9] o.a.n.c.s.StandardControllerServiceNode StandardControllerServiceNode{controllerServiceHolder=org.apache.nifi:nifi-lookup-services-nar:1.10.0-SNAPSHOT, versionedComponentId=null, comment='', processGroup=StandardProcessGroup[identifier=0abd5fbf-016b-1000-00a7-2df537bcba2a], active=true} Failed to invoke @OnEnabled method due to org.apache.nifi.reporting.InitializationException: org.apache.commons.configuration2.ex.ConfigurationException: XML configuration file contained an external entity. To prevent XXE vulnerabilities, NiFi has external entity processing disabled.: {}
org.apache.nifi.reporting.InitializationException: org.apache.commons.configuration2.ex.ConfigurationException: XML configuration file contained an external entity. To prevent XXE vulnerabilities, NiFi has external entity processing disabled.
at org.apache.nifi.lookup.configuration2.CommonsConfigurationLookupService.onEnabled(CommonsConfigurationLookupService.java:121)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:498)
at org.apache.nifi.util.ReflectionUtils.invokeMethodsWithAnnotations(ReflectionUtils.java:142)
at org.apache.nifi.util.ReflectionUtils.invokeMethodsWithAnnotations(ReflectionUtils.java:130)
at org.apache.nifi.util.ReflectionUtils.invokeMethodsWithAnnotations(ReflectionUtils.java:75)
at org.apache.nifi.util.ReflectionUtils.invokeMethodsWithAnnotation(ReflectionUtils.java:52)
at org.apache.nifi.controller.service.StandardControllerServiceNode$2.run(StandardControllerServiceNode.java:435)
at org.apache.nifi.engine.FlowEngine$2.run(FlowEngine.java:110)
at java.util.concurrent.Executors$RunnableAdapter.call(Executors.java:511)
at java.util.concurrent.FutureTask.run(FutureTask.java:266)
at java.util.concurrent.ScheduledThreadPoolExecutor$ScheduledFutureTask.access$201(ScheduledThreadPoolExecutor.java:180)
at java.util.concurrent.ScheduledThreadPoolExecutor$ScheduledFutureTask.run(ScheduledThreadPoolExecutor.java:293)
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
at java.lang.Thread.run(Thread.java:748)
Caused by: org.apache.commons.configuration2.ex.ConfigurationException: XML configuration file contained an external entity. To prevent XXE vulnerabilities, NiFi has external entity processing disabled.
at org.apache.nifi.security.xml.SafeXMLConfiguration.delegateRead(SafeXMLConfiguration.java:139)
at org.apache.nifi.security.xml.SafeXMLConfiguration.read(SafeXMLConfiguration.java:128)
at org.apache.commons.configuration2.io.FileHandler.loadFromStreamDirectly(FileHandler.java:1080)
at org.apache.commons.configuration2.io.FileHandler.loadFromStream(FileHandler.java:1055)
at org.apache.commons.configuration2.io.FileHandler.load(FileHandler.java:990)
at org.apache.commons.configuration2.io.FileHandler.load(FileHandler.java:973)
at org.apache.commons.configuration2.io.FileHandler.load(FileHandler.java:702)
at org.apache.commons.configuration2.builder.FileBasedConfigurationBuilder.initFileHandler(FileBasedConfigurationBuilder.java:312)
at org.apache.commons.configuration2.builder.ReloadingFileBasedConfigurationBuilder.initFileHandler(ReloadingFileBasedConfigurationBuilder.java:185)
at org.apache.commons.configuration2.builder.FileBasedConfigurationBuilder.initResultInstance(FileBasedConfigurationBuilder.java:291)
at org.apache.commons.configuration2.builder.FileBasedConfigurationBuilder.initResultInstance(FileBasedConfigurationBuilder.java:60)
at org.apache.commons.configuration2.builder.BasicConfigurationBuilder.createResult(BasicConfigurationBuilder.java:421)
at org.apache.commons.configuration2.builder.BasicConfigurationBuilder.getConfiguration(BasicConfigurationBuilder.java:285)
at org.apache.nifi.lookup.configuration2.CommonsConfigurationLookupService.onEnabled(CommonsConfigurationLookupService.java:119)
... 17 common frames omitted
Caused by: org.apache.commons.configuration2.ex.ConfigurationException: Error parsing file:/Users/alopresto/Workspace/nifi/nifi-nar-bundles/nifi-standard-bundle/nifi-standard-processors/src/test/resources/xxe_from_report.xml
at org.apache.commons.configuration2.XMLConfiguration.load(XMLConfiguration.java:1030)
at org.apache.commons.configuration2.XMLConfiguration.read(XMLConfiguration.java:996)
at org.apache.nifi.security.xml.SafeXMLConfiguration.lambda$read$1(SafeXMLConfiguration.java:129)
at org.apache.nifi.security.xml.SafeXMLConfiguration.delegateRead(SafeXMLConfiguration.java:135)
... 30 common frames omitted
Caused by: org.xml.sax.SAXParseException: DOCTYPE is disallowed when the feature "http://apache.org/xml/features/disallow-doctype-decl" set to true.
at com.sun.org.apache.xerces.internal.parsers.DOMParser.parse(DOMParser.java:257)
at com.sun.org.apache.xerces.internal.jaxp.DocumentBuilderImpl.parse(DocumentBuilderImpl.java:339)
at org.apache.commons.configuration2.XMLConfiguration.load(XMLConfiguration.java:1023)
... 33 common frames omitted
2019-05-30 14:59:20,529 ERROR [Timer-Driven Process Thread-9] o.a.n.c.s.StandardControllerServiceNode Failed to invoke @OnEnabled method of XMLFileLookupService[id=0abec592-016b-1000-192b-309d4b845a7b] due to org.apache.nifi.reporting.InitializationException: org.apache.commons.configuration2.ex.ConfigurationException: XML configuration file contained an external entity. To prevent XXE vulnerabilities, NiFi has external entity processing disabled.
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
After re-examination, the service stays in Enabling state.
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
It may be better to implement this check as a validator instead. I'll add an XMLValidator which checks for XXEs.
|
I've added an XXE validator to the CommonsConfigurationLookupService to do a simple check if the file contains an !ENTITY declaration. This in combination with the SafeXMLConfiguration will restrict XXE usage in XML configuration files in NiFi. |
|
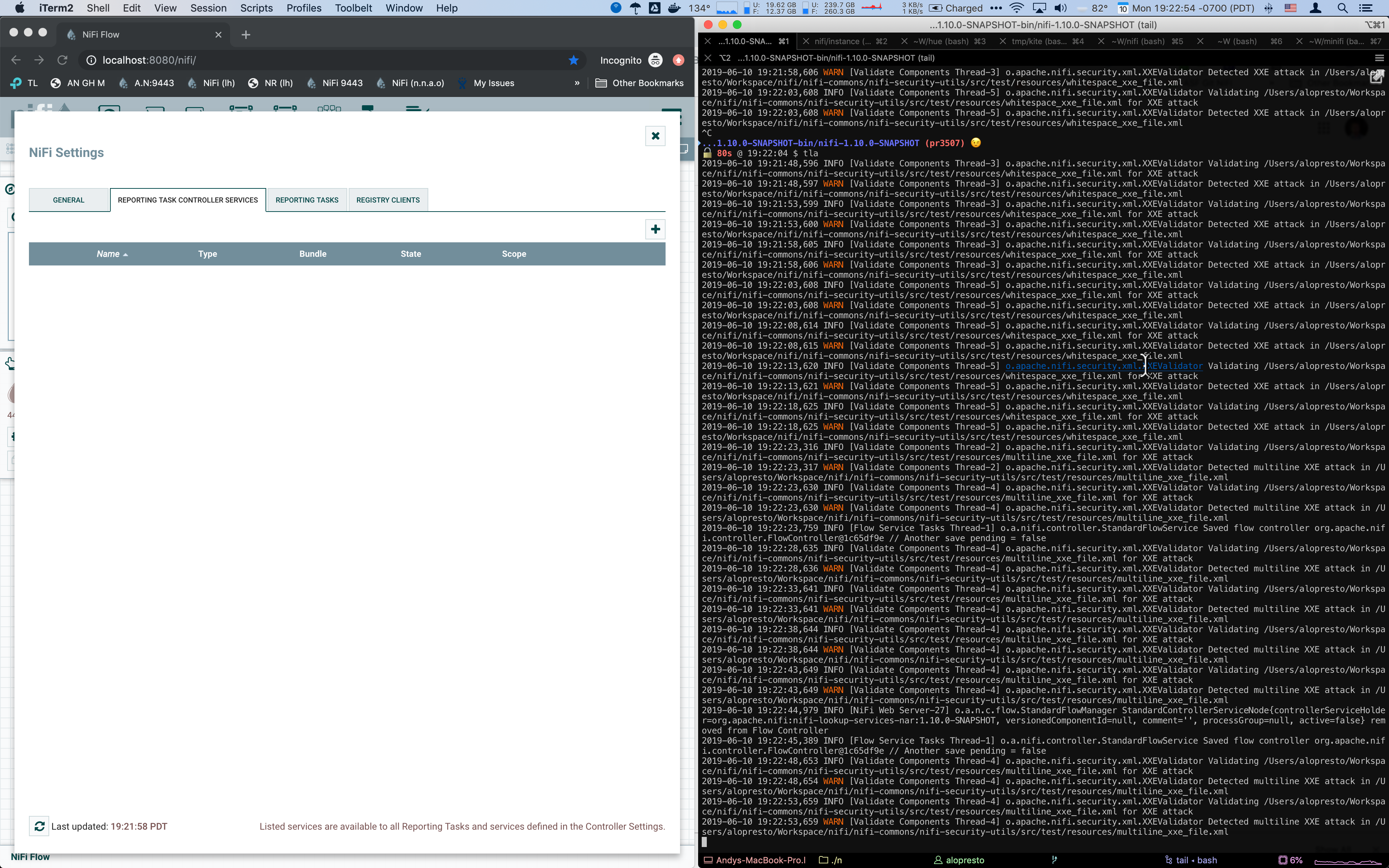
I built the PR successfully and ran a local instance.
I'm going to see if I can enforce the same expected behavior from the regular and whitespace XXE file on the multiline XXE file. I am also going to suppress the stacktrace unless |
|
I was able to modify some code to allow multiline XXE attacks to be caught during validation. I updated the unit tests to accurately reflect this. I discovered another issue -- the |
|
Continuing to investigate. Not sure which timer/thread is triggering the validation, but you can see from the log it continues with cached data even after the controller service is deleted. |
|
Leaving my additional commits here for now: alopresto/nifi/pr3507 |
|
Was testing and had no problem verifying the new behavior in the XMLFileLookupService as a Reporting Task Controller Service: But when I tried to create the controller service on the Process Group level, the UI would hang. Investigated by @mcgilman and this looks to be a result of https://issues.apache.org/jira/browse/NIFI-6341 which was fixed recently. |
…h may call external entities. NIFI-6301 - Fixed unit test. Added comments. NIFI-6301 - Removed unused rule from test. NIFI-6301 - Changed read() methods to use a boolean instead. Updated comments. NIFI-6301 - Fixing checkstyle errors.
…s that contain XXE declarations. Added unit tests and related XML test files.
3ea0668
to
bf4bf26
Compare
Added logging messages. Updated unit test.
|
@alopresto I've verified the issue you had with the validator still running even after the controller service is deleted. It occurs for 'controller level' controller services, and not for process-group scoped controller services. It appears to occur for all validators, as I have tested it with another validator other than the XXE one I have added. I have opened a new Jira to track this issue: https://issues.apache.org/jira/browse/NIFI-6371 |
|
Ran |

…h may call external entities.
NIFI-6301 - Fixed unit test. Added comments.
NIFI-6301 - Removed unused rule from test.
NIFI-6301 - Changed read() methods to use a boolean instead. Updated comments.
NIFI-6301 - Fixing checkstyle errors.
Thank you for submitting a contribution to Apache NiFi.
Please provide a short description of the PR here:
Description of PR
Enables X functionality; fixes bug NIFI-YYYY.
In order to streamline the review of the contribution we ask you
to ensure the following steps have been taken:
For all changes:
Is there a JIRA ticket associated with this PR? Is it referenced
in the commit message?
Does your PR title start with NIFI-XXXX where XXXX is the JIRA number you are trying to resolve? Pay particular attention to the hyphen "-" character.
Has your PR been rebased against the latest commit within the target branch (typically
master)?Is your initial contribution a single, squashed commit? Additional commits in response to PR reviewer feedback should be made on this branch and pushed to allow change tracking. Do not
squashor use--forcewhen pushing to allow for clean monitoring of changes.For code changes:
mvn -Pcontrib-check clean installat the rootnififolder?LICENSEfile, including the mainLICENSEfile undernifi-assembly?NOTICEfile, including the mainNOTICEfile found undernifi-assembly?.displayNamein addition to .name (programmatic access) for each of the new properties?For documentation related changes:
Note:
Please ensure that once the PR is submitted, you check travis-ci for build issues and submit an update to your PR as soon as possible.